Years ago, when a family member or friend had a computer problem, we had to go to his house to try to fix it. But on many occasions this will no longer be necessary thanks to the type of programs that we will talk about here. The aforementioned AnyDesk is one of them, in fact, it could be considered one of the most popular in the sector, a trust that has been earned over time. We can use the portable or installable version of the application to make remote connections with any other computer in the world.
In this way and in a personalized way, we will be able to have control over other equipment remotely without leaving our seat. But as we mentioned before and it is not difficult to imagine, here the security and privacy are key elements. We must bear in mind that in these connections we handle and share an enormous amount of sensitive information. In addition, a potential attacker could take control of said connection, with all the problems that this would entail.
Precisely for all this, this type of program, as with AnyDesk, tries to help us and protect us. So we can establish a series of access keys for each connectionpersonalize the contents that we can use, deactivate the file sharing and other objects etc
Protect your connections in AnyDesk with this change
In fact, in these same lines we are going to talk about a function that is deactivated by default and that will allow us to protect our sessions here in a much more secure way. Specifically, we are referring to the possibility of activating a two-factor authentication for our connection logins. Basically what we achieve by activating this functionality is to ensure that other malicious users cannot carry out saved logins in the program.
To be able to make these remote connections, from that moment on, a second verification and authentication system will be needed to start working with the other remote PC. As we mentioned before, this is something that we find disabled by default in AnyDesk, but that we are going to solve. In order to achieve what we are telling you about, we open the program in a conventional way and access its configuration window.
On the left side of it we find a panel full of sections that we can customize in the software. But the one that interests us in this case is the so-called Security. Here we meet several customizable parametersbut what interests us in this case is found in the section on permissions.
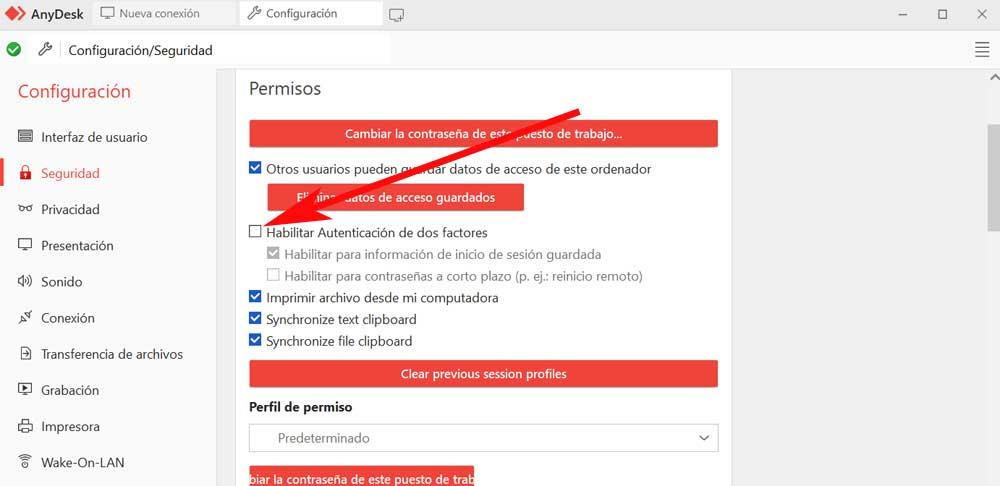
As we can see, the default feature is disabled, so the first thing we do is mark the corresponding selector. In addition, we can enable this two-factor authentication for saved logins and for the passwords short term. This ensures that other malicious users can initiate remote connection sessions without our permission.


