A failure in the DNS system could affect millions of IoT devices, seriously compromising their security.
We live in an increasingly connected world. In fact, in recent years the presence of the so-called Internet of Things (IoT) has increased the number of connected devices used in homes and businesses. Now if the security of this type of device is compromisedit can become dangerous.
In fact, it has recently been discovered that a new security breach is starting to be used that affects this type of device through the DNS system. In this way, devices that synchronize information with the Internet could be seized by attackers under certain circumstances, putting their safety in doubt.
Millions of connected devices may be affected by a security threat that has not yet been fixed
As we mentioned, according to a new study by Nozomi Networksit seems that back in September 2021 a possible security threat over bookstores uClibc Y uClibc-ng of the programming language C. These libraries are quite common, but in reality until now the true dangers of these threats were not known, and they seem to be starting to spread. be implemented by attackers.
Millions of IoT devices will be affected by the vulnerability of the libraries of C
Apparently, through these vulnerabilities it is possible that attackers perform “DNS poisoning”, that is, an attack on the domain name system cache. DNS allows Internet names to be translated to IP addresses of servers and, if the cache is altered, it is possible change the destination server to a fake one to which the device transmits the information, as explained by Giannis Tsaraias and Andrea Palanca:
“The issue is caused by the predictability of the transaction IDs included in the DNS requests generated by the library, which may allow attackers to perform “DNS poisoning” attacks against the target device.”
Although they are not the only ones, devices connected to the Internet of Things (IoT) They are some of the most affected by this type of failure, and those that pose a greater danger today. If, for example, the destination server for the information of a security camera is altered, the attacker may have the possibility of access all information of the same, being able to reproduce the content.
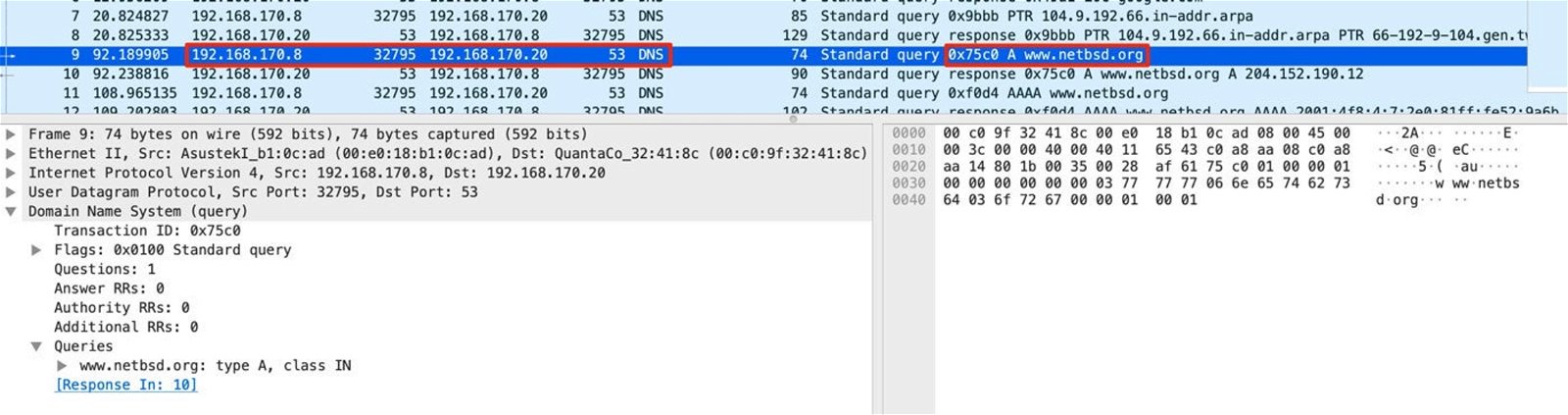
This is how “DNS poisoning” attacks work and can be very dangerous on IoT devices. Image: Nozomi Networks
However, what is most worrying is that, although the security flaw was discovered in September last year, has not been solved yet. From Nozomi Networks are already collaborating with the developers of the libraries of C mentioned above in order to find a solutionbut at the moment it seems that it has not been possible.
In the meantime, the only recommendation is to use the DNSSEC standard, which ensures that the destination server corresponds to what it really should be. However, its implementation at a technical level is somewhat more delicate, taking into account that both the devices and the servers must be adapted for everything to work properly, and this is something that is not always so simple.
Related topics: Security
Share


